In India, more than five cases of cybercrime are reported on an average every hour, according to the statistics compiled by the National Crime Records Bureau (NCRB). The Bureau, under the Ministry of Home Affairs, is responsible for collecting and analysing crime data as per the Indian Penal Code (IPC) and Special and Local Laws (SLL).
- Praveen recently retired after working at a public sector undertaking in a senior position. He invested his savings in various schemes in a nationalised bank and also put some money into retail business. In late April, he received a call from an unknown number saying that his electricity bill was due and if not paid immediately, supply would be terminated. The caller advised him to log into a website while on the call and start the process of payment. He realised something was wrong and disconnected. He then checked and found he had no pending bill.
- Parag received a mail from his bank seeking some details of a payment he had made a few days earlier. He clicked on the mail without noticing that it had been generated from a free mail server and not the official one. The mail had an attachment, he opened it and filled in the required information and sent it back. Soon he found that his bank account had been drained of a significant sum.
- Rimi wanted to make an online payment to a service provider. When she typed the initial letters of the name of the company, the full name popped up by itself. Believing that the search engine had prompted the full name, she clicked on it. She noticed a few changes on the website but assumed that the company was working on a makeover, and went on with her payment. Unknown to her, the website was actually managed by a scamster, who would monitor every click, every bit of information for days to come by surreptitiously planting malware in her computer.
(The names of cybercrime victims have been changed to protect their identity.)
According to its report, “Crime in India – 2020”, a total of 50,035 cases were registered under cybercrime, showing an increase of 11.8% over 2019, when 44,735 cases were reported. During 2020, 60.2% of cybercrime cases registered were for the motive of fraud, followed by 6.6% cases of sexual exploitation (3,293 cases). There were 2,440 cases of extortion, accounting for 4.9% of recorded cases.
In metros, considering cities with populations of more than two million, 18,657 cases were registered under various types of cybercrime, showing an increase of 0.8% over 2019, when 18,500 cases were reported. The cybercrime rate increased from 16.2% in 2019 to 16.4% in 2020. Most cases of cybercrime were reported from Ahmedabad, Bengaluru, Chennai, Coimbatore, Delhi, Ghaziabad, Hyderabad, Indore, Jaipur, Kanpur, Kochi, Kolkata, Kozhikode, Lucknow, Mumbai, Nagpur, Patna, Pune and Surat. Among the cases reported, computer-related offences (Section 66 of the IT Act) totalled 11,356 and formed the highest number of cybercrime cases—accounting for 60.9%—in 2020.
The highlight of the report is that cybercrime increased by 306% in the past four years. India’s cybercrime rate—or the number of cybercrimes per one lakh of the population—went up 270% in the past four years. The NCRB data also shows that on an average, 65.81% of cases were pending investigation at the end of each year. An average 45.57% of cases taken up for investigation in a particular year were those that were pending investigation from the previous year. In 2016, 24,187 cybercrime cases for investigation included a spillover of 11,870 cases from the previous year. Of these, 14,973 cases were pending investigation at the end of the year and 9,213 were disposed of by the police. In 2020, the cases reported for investigation increased to 1,03,000 and 51.1% (or 53,157 cases) were carried forward from the previous year.
A bad joke
Over the past few years, there has been an alarming spurt in breach of cybersecurity of government as well as private entities. Answering a question in the Rajya Sabha on April 1, Minister of State for Electronics and Information Technology Rajeev Chandrasekhar stated: “CERT-In (Indian Computer Emergency Response Team) has reported that a total number of 5461, 33514, 70798, 85797, 54314 and 48,285 cybersecurity incidents related to government organisations during the years 2016, 2017, 2018, 2019, 2020 and 2021, respectively.” He added, “There are attempts from time to time to launch cyberattacks on Indian cyberspace. It is observed that attackers compromise computer systems located in different parts of the world and use masquerading techniques and hidden servers to hide the identity of actual systems from which the attacks are launched.”

This year, the Twitter accounts of the Prime Minister’s Office, the University Grants Commission, the Indian Meteorological Department (IMD) and the Uttar Pradesh Chief Minister’s Office were among the several high-profile accounts that were hacked briefly. Government data mentions the hacking of over 600 social media accounts of the central government in the past five years.
Cybersecurity experts believe that cyberattacks are generally aimed at a country’s administrative or military handles and critical information infrastructure not only to cull out sensitive data but also to create a feeling of distrust and mistrust among people. Despite the fact that such attacks are sooner or later repelled effectively, a sense of uncertainty over personal information stored with the government begins to grow.
Following a spate of cyber breach reports, CERT-In issued a circular asking all service providers, intermediaries, data centres, corporates and government organisations to mandatorily enable logs of all their information and communication technology systems and maintain them securely for a rolling period of 180 days. CERT-In serves as the national agency for performing various functions in the cybersecurity domain as per provisions of Section 70B of the Information Technology Act, 2000. It analyses cyber threats and handles cyber incidents reported to it. CERT-In regularly issues advisories to organisations and other users to enable them to protect their data or information and ICT (information and communications technology) infrastructure and systems. To coordinate response activities as well as emergency measures with respect to cybersecurity incidents, CERT-In calls for information from service providers, intermediaries, data centres and the body corporate.
The NCRB data also shows that on an average, 65.81% of cases were pending investigation at the end of each year. An average 45.57% of cases taken up for investigation in a particular year were pending from the previous year
The circular, dated April 28, says, “During the course of handling cyber incidents and interactions with the constituency, CERT-In has identified certain gaps causing hindrance in incident analysis. To address the identified gaps and issues so as to facilitate incident response measures, CERT-In has issued directions relating to information security practices, procedure, prevention, response and reporting of cyber incidents under the provisions of sub-section (6) of section 70B of the Information Technology Act, 2000. These directions will become effective after 60 days.
“The directions cover aspects relating to synchronization of ICT system clocks; mandatory reporting of cyber incidents to CERT-In; maintenance of logs of ICT systems; subscriber/customer registrations details by Data centres, Virtual Private Server (VPS) providers, VPN Service providers, Cloud service providers; KYC norms and practices by virtual asset service providers, virtual asset exchange providers and custodian wallet providers. These directions shall enhance overall cybersecurity posture and ensure safe and trusted Internet in the country.”
However, independent cybersecurity experts say that the latest CERT-In directive doesn’t amount to much when it comes to protecting the national cyberinfrastructure. Instead, they point out that it’s highly intrusive, designed to prey on the country’s citizens and will increase the state’s surveillance powers. Cyber experts told the technology monitoring website, Medianama, that the new directions are a “bad joke” and published a long list of serious flaws of the mandate, including some that are virtually impossible to implement.
Many types of cybercrime
Answering another question in the Lok Sabha on April 6, Chandrashekar stated, “The Government is committed to ensuring that the internet in India is open, safe and trusted and accountable for all users. Indian Computer Emergency Response Team (CERT-In) is mandated to track and monitor cyber security incidents in India. CERT-In has reported that a total number of 1,402,809 & 212,485 cyber security incidents are observed during the years 2021 & 2022 (upto February) respectively.” Earlier, on March 30, the minister informed Parliament that “As per CERT-In, a total number of 552, 454, 472, 280, and 523 phishing incidents were observed during the years 2017, 2018, 2019, 2020 and 2021 respectively. Further, a total number of 56, 30, 43, 54 and 132 ransomware incidents were observed during the years 2017, 2018, 2019, 2020 and 2021 respectively.”

As evident from the instances provided at the beginning of this article, many cybercrime incidents go either undetected or unreported. Sometimes, small amounts of money are siphoned from compromised accounts over a period of time making detection difficult, say cybersecurity experts. Elderly persons and first-generation users appear to be the most vulnerable, mainly due to inadequate knowledge of cybersecurity and internet hygiene. For such users, it may be difficult to understand if a transaction is happening with an authorised site or person or if a fraud is siphoning off money.
Cybersecurity experts believe that cyberattacks are generally aimed at a country’s administrative or military handles and critical information infrastructure not only to cull out sensitive data but also to create a feeling of distrust
However, even IT professionals and people with decent knowledge of the web have been victims of cybercrime. Women are also among the vulnerable target group, where online fraudsters first establish a virtual relationship with the target and then request money transfer for “customs clearance of gifts”. Similarly, the youth are scammed with job or “professional loan” offers. Middle-aged citizens, whether working or retired, are often victims of KYC (Know Your Customer) scams or other supportive information.
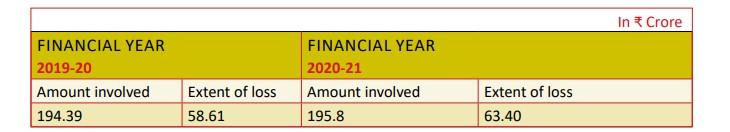
A government statement in Parliament on March 29 assessed the financial loss to cybercrime victims. The minister of state in the Ministry of Finance, Bhagwat Karad, stated: “The Reserve Bank of India (RBI) is the regulator and supervisor of the banking system. RBI had apprised that it does not maintain data on financial loss caused due to cyber-crimes to individuals having accounts in banks. RBI has further informed that the year-wise extent of loss in frauds in the category ‘Card/Internet – ATM/Debit Card, Credit Card and Internet Banking’, based on the date of reporting by Public Sector Banks (which consist of nationalised banks and the State Bank of India) and private sector banks, for the last two financial years, is as below:
(see table)
Criminals also exploited the anxiety and uncertainty prevalent during the initial stages of the Covid-19 pandemic by luring many citizens with promises of medicines, oxygen, and vaccination delivery over emails and calls. During the lockdown, scamsters robbed people online on the pretext of delivering alcohol. In July 2021, the Maharashtra Cyber Cell traced an accused to Saharanpur in Uttar Pradesh for duping veteran actor Shabana Azmi in a phishing scam. Azmi posted on Twitter how an alcohol delivery platform took money “upfront and when the ordered item didn’t turn up they stopped picking up my calls” (sic).
According to a report in Deccan Herald, quoting a senior police official with the Cyber, Economic and Narcotics (CEN) Crime Police Station, Bengaluru is a hub of victims and not cybercriminals. Most perpetrators are based in Uttar Pradesh, Bharatpur (Rajasthan), Jamtara (Jharkhand) and Pune (Maharashtra). According to the officer, “almost 90% of the accused persons are in north India”. So much has been said about criminal groups of Jamtara and their skill in convincing individuals to part with credit card details, KYC, or pin codes and other personal details, that a web series has been made with the same name as the district. Unfortunately, it may not be known to many that Jamtara has become the only district in the country where all gram panchayats have community libraries. The district has a population of about eight lakh with 118 village panchayats under six blocks. Career counselling sessions and motivational classes are also held for free at these places. Earlier, it was said that lack of education and scarcity of books led youngsters into crime.
So much has been said about criminal groups of Jamtara and their skill in convincing individuals to part with credit card details, KYC, or pin codes and other personal details, that a web series has been made
However, it is not only government or administrative sites and social media handles or individual users who are targets for hackers. A study published in September 2021, titled “Cybersecurity for SMBs: Asia Pacific Businesses Prepare for Digital Defense”, by CISCO found that “more than half (56%) of Asia Pacific SMBs (small and medium-sized businesses) experienced a cyber incident in the past year with many falling victim to cybercrime—85% suffered a malware attack. As a result of these incidents, malicious actors are getting their hands on valuable data ranging from customer information (75%), internal emails (62%), employee data (61%) to intellectual property (61%) and financial details (61%)”.
The study added: “This is having a tangible impact on SMBs with 62% of respondents saying a cyber incident disrupted their operations and 61% noting that it resulted in a loss of revenue.
“In addition, 57% saw a loss of trust with customers, while 66% said that a cyber incident affected the company’s reputation negatively. Though unquantifiable, a decline in reputation and erosion of trust can have disastrous consequences for any business.”
Personal data privacy
About a year ago, hackers uploaded personally identifiable data of about 20 million users from an online grocery store in India. The data comprised various identifiable points like phone numbers, email IDs, passwords, delivery addresses, order details. Such details of customers are known to be “auctioned” on the dark web. Data is the identifier of an individual on the internet or in the virtual world. “It’s my property… data fiduciary or data processor should take as much information as needed for a particular transaction and then delete it. There has to be a principle of proportionality,” says senior counsel Vivek Sood, who has authored several books on cyber laws. “In the (Justice K.S.) Puttaswamy case, the Supreme Court has recognised Right to Privacy as a Fundamental Right, being part and parcel of Article 21 of the Constitution of India.

“Right to Privacy is now part of Right to Life and Liberty. Having done that, the Supreme Court has left it to the legislative will to operationalise Right to Privacy as legislation. We have the Personal Data Protection Bill, 2019, which is still pending…. I’m sure the government is working on it and hope it is converted into law in the near future.”
The Personal Data Protection Bill, 2019 has clearly stated the obligations of a data fiduciary. A data fiduciary is an entity or individual who decides the means and purpose of processing personal data. Such processing will be subject to certain purpose, collection, and storage limitations. For instance, personal data can be processed only for specific, clear, and lawful purposes. Additionally, all data fiduciaries must undertake certain transparency and accountability measures such as implementing security safeguards (such as data encryption and preventing misuse of data), and instituting grievance redressal mechanisms to address complaints of individuals. They must also institute mechanisms for age verification and parental consent when processing sensitive personal data of children.
About a year ago, hackers uploaded personally identifiable data of about 20 million users from an online grocery store in India. The data comprised various identifiable points like phone numbers, email IDs, delivery address, etc
The bill was introduced in the Lok Sabha by the then minister for electronics and information technology, Ravi Shankar Prasad, on December 11, 2019. It seeks to provide for the protection of the personal data of individuals and establishes a Data Protection Authority for the same. “It is a well-drafted Bill but is yet to be converted into law. I have analysed the Bill in my book, Right To Privacy: Arguing For The People,” says Sood.
In the section on how privacy is being compromised by the digital footprints of customers, the author writes, “Massive profiling of individuals is taking place in the virtual world by commercial enterprises for targeted advertising and for providing services by understanding the consumers’ past behaviour and transactions. In this competitive world of e-commerce, commercial enterprises are scrambling to be ahead of rivals and thus to provide the ‘best’ experience to consumers, profiling is happening on an unimaginable scale. In this spirit of competition, the right to the informational privacy of individuals is being compromised. This is against principles laid down in Puttaswamy judgement and the Information Technology Act 2000.”
A Central Information Commission report on the Right to Privacy noted, “The sphere of privacy includes a right to protect one’s identity. The right recognises the fact that all information about a person is fundamentally her own, and she is free to communicate or retain it to herself. The core of informational privacy, thus, is a right to autonomy and self-determination in respect of one’s personal data.”
In his book, Sood reflects upon issues like the significance of the Right to Privacy in the age of the internet, the Toolkit and Pegasus controversies, and the vulnerabilities of the Aadhaar scheme.
The Pegasus Project
In October 2019, journalist Ashish Gupta came to know that he had been hacked when he received a call from Citizen Lab, a University of Toronto-based tech research facility. “They asked me if I was aware my mobile phone had been hacked. I had some idea about surveillance and bugging, but hadn’t specifically known what Pegasus does,” he said.
According to a CBC report, Israel-based NSO group’s Pegasus spyware has been used around the world to break into the phones and computers of human rights activists, journalists, and even Catholic clergy. The firm has been subject to export limits by the US federal government, which has accused NSO of conducting “transnational repression”. NSO has also been taken to court by major technology companies, including Apple and Meta, the owner of WhatsApp.
The SolarWinds cyberattack is dubbed among the world’s largest supply chain based cyberattacks, where alleged Russian attackers reportedly hacked and spied on the US government. It was one of the most sophisticated hacks

The report added, “Citizen Lab said its investigations into the use in Spain of Pegasus and spyware developed by Candiru—another Israeli firm founded by former NSO employees—started in late 2019 after a handful of cases targeting high-profile Catalan pro-independence individuals were revealed.”
RISING CONCERN OVER CYBERSECURITY
Some of the India-specific top-line findings of the “Cybersecurity for SMBs: Asia Pacific Businesses Prepare for Digital Defense” report
84%
of SMBs are more worried about cybersecurity now than a year ago.
74%
of SMBs in India have had a cybersecurity incident in the past 12 months.
84%
of SMBs in India agree that a serious cybersecurity incident could mean the end of their organisation.
85%
of those in India that suffered a cyber incident lost customer information.
76%
of those in India that suffered a cyber incident had their reputation negatively affected.
74%
of those in India that suffered a cyber incident lost revenue.
36%
of SMBs in India said the number one reason behind suffering cyber incidents was that their cybersecurity solutions were inadequate.
38%
of SMBs in India ranked not having cybersecurity solutions as the number one reason for suffering cybersecurity incidents.
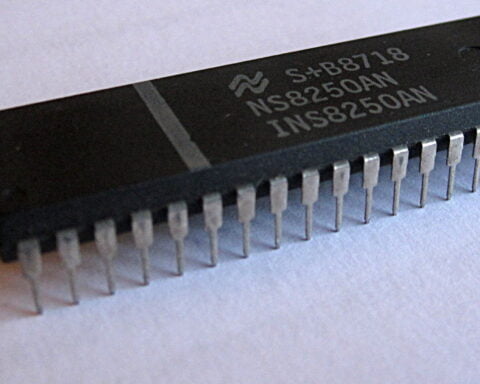
While the Pegasus project underlined the vulnerability of smartphones, the SolarWinds issue revealed how IT software could be used to hack into company and government networks. The SolarWinds cyberattack is dubbed among the world’s largest supply chain based cyberattacks, where alleged Russian attackers reportedly hacked and spied on the US government. The hackers made use of a vulnerability in a product made by Texas-based SolarWinds Corp, whose software was popular with many enterprises.
In India, it was the NSO ‘spyware’ that created a stir. The Pegasus software costs millions of dollars and is licensed for use only by governments. The spyware was special with its ability to hack into any phone easily and give the hacker total access and control.
In July last year, news portal The Wire broke the Pegasus investigation that was carried out in collaboration with 17 news organisations involving 80 journalists across 10 countries. It exposed the pervasive use of the weapon-grade software to hack the phones of activists, journalists, opposition leaders, ministers, and constitutional authorities, among others. The phone numbers of Indian ministers, opposition leaders, former election commissioners and journalists were found on an NSO database. Reports also suggested that the Koregaon Bhima activists had the surveillance software implanted on their phones and their numbers were found on the Pegasus database. Earlier, a US-based digital forensic firm, Arsenal Consulting, released two detailed reports, which are now part of the legal proceedings, in which they alleged that the computers of some of the key activists were compromised, using a commercially available malware that was used to plant evidence on their systems remotely.
Pegasus revelations began in mid-2021, with the Paris-based Forbidden Stories and other media organisations, including The Wire in India, reporting how the spyware was being used by governments across the world to stifle dissent. “The process of surveillance in civic life undermines democratic rights and yet goes on across the world. Can you imagine, that surveillance agencies are developing and selling coronavirus tracking technology? The NSO Group too has the dubious record of selling such technology to different governments, which do not acknowledge any obligation to honour the democratic rights of their citizens. This company is now selling an extensive data analysis tool, claiming that the device tracks the spread of corona infection by mapping human movements,” says Gupta.
Pegasus revelations began in mid-2021, with the Paris-based Forbidden Stories and other media organisations, including The Wire in India, reporting how the spyware was being used across the world to stifle dissent
On its official site, NSO claims it “creates technology that helps government agencies prevent and investigate terrorism and crime to save thousands of lives around the globe”. As per the product manual, which has been reviewed by Tatsat Chronicle, “Pegasus is a world-leading cyber intelligence solution that enables law enforcement and intelligence agencies to remotely and covertly extract valuable intelligence from virtually any mobile device”.
In 2020, concerns were raised when New York-based tech company Clearview AI was in talks with US authorities for helping trace the spread of the coronavirus. Clearview AI is an American facial recognition company, providing software to companies, law enforcement, universities, and individuals. Its algorithm matches face to a database of reportedly over three billion images indexed from the web, including social media applications. Involved in a case accusing it of collecting people’s photographs without their permission, it recently agreed to restrictions on how businesses can use its database. The company will stop granting paid or free access to the data to most private businesses and individuals. However, Clearview AI can still work with federal government agencies—including immigration authorities—and state government agencies outside Illinois, where it is headquartered.
In India, opposition parties and a section of activists had raised a hue and cry over the Aarogya Setu App that was used to track Covid patients. However, downloading the app is voluntary. Digital rights activists pointed out that very little was known about the developers of the app or how the collected personal data was being stored and secured. Whenever downloading an app, attention needs to be paid to its authenticity and source of origin, the folders it is seeking permission to use and why, as well as its history. While using a computer or a mobile phone it is pertinent that we use basic caution, cyber hygiene and common sense to keep ourselves safe.